How CrowdStrike’s 78-minute outage reshaped enterprise cybersecurity
The CrowdStrike incident that occurred on July 19, 2024, served as a stark reminder of the importance of cyber resilience. One year later, CrowdStrike, along with the entire industry, has undergone significant transformation following the 78-minute outage that changed everything.
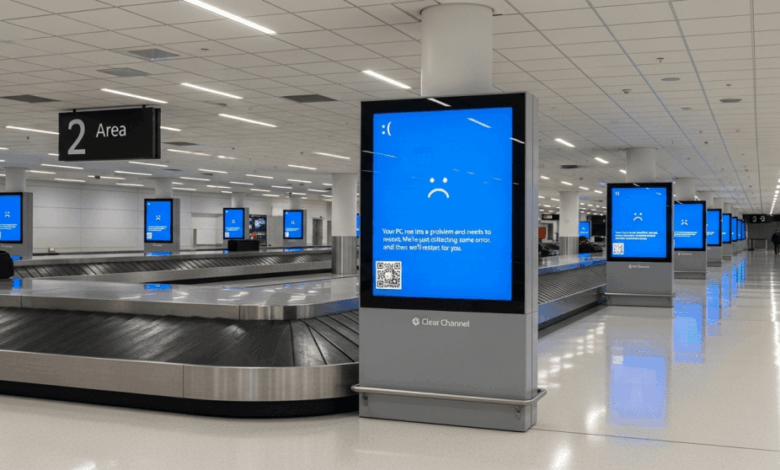
CrowdStrike’s President, Mike Sentonas, reflected on the impact of the incident in a blog post, highlighting how it became a defining moment in the company’s history. The faulty Channel File 291 update, deployed and reverted within 78 minutes, resulted in the crash of 8.5 million Windows systems globally, causing significant financial losses and disruptions in various sectors, particularly aviation.
Steffen Schreier, from Telesign, emphasized the far-reaching consequences of the incident, noting that even routine software updates can have catastrophic effects on global infrastructure due to internal failures.
The root cause analysis revealed technical failures in CrowdStrike’s systems, exposing fundamental quality control gaps. Merritt Baer, from Enkrypt AI, pointed out the importance of implementing basic CI/CD protocols to prevent such incidents in the future.
CrowdStrike’s founder and CEO, George Kurtz, took ownership of the incident, emphasizing the company’s commitment to building a stronger and more resilient platform. The company introduced the Resilient by Design framework, focusing on foundational, adaptive, and continuous improvements in their security operations.
The incident prompted a broader discussion on vendor dependencies and the need for enhanced security protocols in supplier relationships. Industry experts, like Sam Curry from Zscaler, highlighted the importance of resilience and security in the wake of the CrowdStrike incident.
Schreier underscored the need for a new security paradigm that prioritizes safeguards and fail-safes to prevent systemic failures. Looking ahead, Baer discussed the emergence of AI-driven security solutions and the importance of autonomy in infrastructure decision-making.
CrowdStrike’s initiatives post-incident include hiring a Chief Resilience Officer, exploring new capabilities, collaborating with Microsoft, and obtaining certifications for business continuity management.
The incident’s legacy extends beyond CrowdStrike, influencing how organizations approach security, vendor relationships, and resilience planning. Sentonas emphasized the ongoing commitment to resilience as a discipline that requires continuous evolution.
In conclusion, the CrowdStrike incident of July 19, 2024, catalyzed an industry-wide evolution towards true resilience. The lessons learned from this incident have led to a deeper understanding of the importance of protecting against threats and ensuring the reliability of security tools. CrowdStrike and the broader security ecosystem have emerged stronger and more prepared to face future challenges.





